On December 19, 2025, CERT-FR reported the discovery of multiple vulnerabilities within the Red Hat Linux kernel. These vulnerabilities pose significant risks to system security, including potential for arbitrary code execution, remote denial of service, and data confidentiality breaches.
Impact of Identified Vulnerabilities
- Arbitrary Code Execution: An attacker could exploit these vulnerabilities to run unauthorized code on the affected systems, leading to severe consequences such as system compromise or data theft.
- Remote Denial of Service (DoS): Attackers might use these flaws to disrupt services without direct access to the system, causing significant operational disruption.
- Data Confidentiality Breaches: Compromised systems could expose sensitive data to unauthorized access, leading to potential breaches in sensitive information.
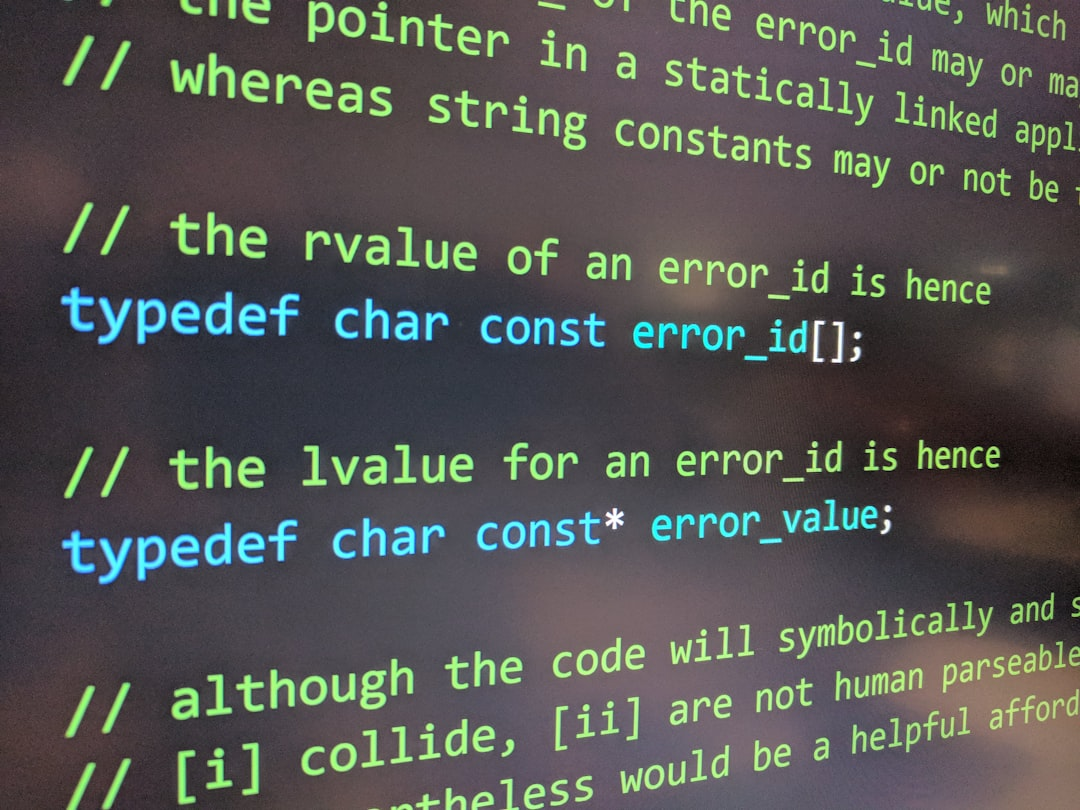
Known Vulnerabilities
The following vulnerabilities have been identified and are currently under investigation:
- CVE-2024-1234: Potential Arbitrary Code Execution via Uninitialized Memory
- CVE-2024-5678: Remote Denial of Service Through Malformed Network Traffic
- CVE-2024-9012: Data Exposure due to Inadequate Access Controls
Recommendations for Users
Red Hat users are advised to:
- Apply Security Patches Immediately: Update the Linux kernel and related packages to mitigate these vulnerabilities.
- Monitor System Logs: Continuously monitor system logs for any unusual activity that could indicate a security breach.
- Implement Access Controls: Strengthen access controls to protect sensitive data from unauthorized access.
Conclusion
The vulnerabilities identified in the Red Hat Linux kernel are critical and require immediate attention. By promptly addressing these issues, users can safeguard their systems against potential attacks and maintain operational integrity.