Summary: A critical vulnerability has been discovered in Google Fast Pair implementations used by millions of Bluetooth audio accessories, leaving them susceptible to hijacking attacks. This issue could potentially compromise the security and privacy of users.
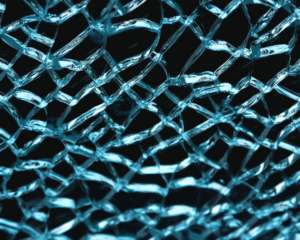
Understanding WhisperPair Attack
The WhisperPair attack targets devices that use Google’s Fast Pair feature for quick pairing with a smartphone or other device. This vulnerability arises from improper implementation of the Fast Pair protocol, allowing attackers to intercept and manipulate Bluetooth connections.
Critical Implications
- Unauthorized access to audio data, potentially exposing personal conversations
- Possibility of unauthorized device control, leading to potential misuse or theft
- Impact on users’ peace of mind and data security
Security Implications
The attack can compromise the security of Bluetooth audio accessories, potentially allowing attackers to intercept and manipulate audio streams. This could lead to eavesdropping, unauthorized device control, or other malicious activities.
CVE IDs
Threat Type and Criticality Score
Threat Type: Vulnerability
Criticality Score: 7/10
Mitigation Measures
- Update firmware and software to patch the vulnerability
- Disable Fast Pair feature if it is not necessary
- Avoid pairing devices in public areas where security is compromised
Conclusion
The WhisperPair attack highlights a critical security flaw affecting millions of Bluetooth audio accessories. Users should be aware of this vulnerability and take appropriate measures to protect their data and privacy.